Title search results
Showing 141 - 160 of 45689 items

Stealing MySpace: the battle to control the most popular website in America
By Julia Angwin. 2009
Pulitzer Prize-winning journalist traces the founding of MySpace.com from its conception as a data-storage site by marketing executives Chris DeWolfe…
and Tom Anderson. Chronicles the business's evolution, lawsuits, and rivalries, which ultimately led to the social-networking web site being purchased by Rupert Murdoch for nearly $600 million in 2005. 2009
Autonomy: the quest to build the driverless car-- and how it will reshape our world
By Christopher Shulgan, Lawrence D. Burns. 2018
In Autonomy, former GM executive and current advisor to the Google Self-Driving Car project Lawrence Burns offers a sweeping history…
of the race to make the driverless car a reality. In the past decade, titans of the old automobile industry, like General Motors, have been partnering with robust tech startups, such as Tesla and Uber, to revolutionize the way we move around the world. It's not a question of whether the self-driving car will disrupt the automobile industry, it's a question of when, how, and who will do it
Data for the people: how to make our post-privacy economy work for you
By Andreas Weigend, Andreas S Weigend. 2017
Every time we do something on the internet, we create data that businesses collect and use to make decisions about…
us. In some ways, it makes life easier, enabling us to integrate maps, send email, or conduct business online, but as individuals, we do not benefit from this wealth of data as much as we could. It is more likely that the data will be used against us rather than for us. Author Weigend says we need to take control of our data to make it work for us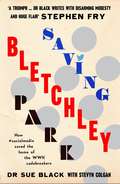
Saving Bletchley Park
By Sue Black. 2013
In 1939, Alan Turing's Bombe machine--the most advanced method used to crack the Nazis' Enigma code--was born at Bletchely Park.…
But at the turn of the 21st Century, the buildings and huts, where teams of codebreakers changed the course of WWII, were crumbling to the ground. This is the story of the fight to save Bletchley Park, the birthplace of modern computing, and the remarkable men and women whose work made it a place worth rescuing
Minecraft: The Unlikely Tale of Markus "Notch" Persson and the Game That Changed Everything
By Jennifer Hawkins, Daniel Goldberg, Linus Larsson. 2017
A completely unique and in-depth look at the creator of Minecraft, Markus "Notch" Persson, and his rise from unknown computer…
programmer to multi-millionaire international gaming icon. Some strong language. For grades 5-8
Disruption: Intelligence artificielle, fin du salariat, humanité augmentée (Documents et essais)
By Stéphane Mallard. 2019
Disruption. Mélange de rupture et de révolution, à la fois rapide, brutale et inéluctable. Ce terme qualifie de plus en…
plus l'époque actuelle, propulsée par les progrès technologiques. Des secteurs entiers, établis solidement depuis des années, disparaissent très rapidement, remplacés par des acteurs plus petits, plus agiles, plus efficaces, moins chers, moins arrogants. Ces acteurs de la disruption, nous les connaissons : ce sont Uber, Airbnb, Netflix, et bien d'autres. Tout est disruptable : les entreprises et leurs services, mais aussi nos modèles d'organisation, nos manières de penser, de communiquer, de travailler, nos valeurs et jusqu'à notre propre corps. Face à la puissance de cette vague qui balaie tout sur son passage, il est urgent de comprendre les nouveaux codes exigés par la disruption, et de se disrupter soi-même pour ne pas disparaître. Sur un ton libre et enthousiasmant, ce livre donne les clés pour comprendre le monde en train de naître, ne pas le craindre, et s'y engager, pour éviter que d'autres ne le bâtissent à notre place. Une lecture dynamique et incarnée par l'auteur lui-même, un des plus grands spécialistes de la transformation digitale
Identity theft is the fastest-growing category of crime in the United States today, and dealing with privacy and identity issues…
has become an essential part of life in our modern society. Each chapter in The Identity Theft Protection Guide contains a self-quiz to identify personal areas of concern, information to help you "take action," and more
Enchanted objects: design, human desire, and the Internet of things
By David Rose. 2014

Virtually you: the dangerous powers of the e-personality
By Elias Aboujaoude. 2011

Four computer nerd undergrads wanted to build a social network that would allow users to control the information they shared,…
instead of surrendering their privacy to big businesses like Facebook. Their project was called Diaspora. Unrated
The invention of voice mail plus other memoirs and essay
By David P. Andersen. 2013
David P. Andersen started writing some years ago after retiring from his life as a computer design engineer. Fascinated by…
a wide variety of topics, he writes on work, cats, his relatives, life in India, and much more
Changing the subject: art and attention in the Internet age
By Sven Birkerts. 2015
Over the last two decades, Sven Birkerts has recognized how the digital world affects the way that we read literature…
and experience art. He believes an unprecedented shift is underway toward distraction, lost of personal agency and an increasing acceptance of hive behaviors. This transformation is more accelerated and more psychologically formative than any previous technological innovation
How the Internet became commercial: innovation, privatization, and the birth of a new network (The Kauffman Foundation Series on Innovation and Entrepreneurship Ser.)
By Shane Greenstein, Shane M Greenstein. 2015
In less than a decade, the Internet went from being a series of loosely connected networks used by universities and…
the military to the powerful commercial engine it is today. There were many of the key innovations that made this possible came from entrepreneurs and iconoclasts who were outside the mainstream. At its outset, the commercialization of the Internet was by no means a foregone conclusion
Kingpin: how one hacker took over the billion-dollar cybercrime underground
By Kevin Poulsen. 2011
Former hacker Kevin Poulsen has, over the past decade, built a reputation as one of the top investigative reporters on…
the cybercrime beat. In Kingpin, he pours his unmatched access and expertise into book form for the first time, delivering a gripping cat-and-mouse narrative and an unprecedented view into the twenty-first century's form of organized crime. Contains strong language
A true crime story, from 1997 to 2011, set in Missoula, Montana, and Costa Rica. University of Montana students turned…
a weekly poker game into an online poker company. There were no government cyber regulations at this time. When creating U.S. laws to regulate online companies, this company and others became targets. Some descriptions of sex and strong language
Your data, their billions: Unraveling and simplifying big tech
By Jane S Hoffman. 2022
What if somebody knew everything about you? Somebody does. That somebody is "Big Tech." Facebook, Google, Amazon, Apple, and Microsoft…
know more about you than you do. And they make billions of dollars by cashing in on your private data. Our personal data, which Big Tech companies get for free, is the engine that drives the unregulated, free-for-all world called the digital marketplace. These corporate giants may bring us information and entertainment, convenience and connection, but they also do a lot of harm. So, what can we do about it? This eye-opening book provides vital information that has been out of reach to those who need it most-the millions of Facebook, Google, Amazon, Apple, and Microsoft users who have come to love and depend upon these digital products. Veteran consumer advocate Jane Hoffman makes the complex world of Big Tech simple to grasp as she reveals exactly how Big Tech uses-and abuses-your personal information. And she proposes a bold blueprint for reforming these corporate behemoths. Your Data, Their Billions is a guidebook to everything at stake in our digital society, from Big Tech's overreach into our daily lives to its practices that threaten our democracy
Windows 7 for seniors for dummies
By Mark Justice Hinton. 2009
Guide to Microsoft's Windows 7 operating system explains using the desktop, creating and organizing documents, connecting to the Internet, playing…
games, watching movies, and protecting your computer and data. Describes the parts of a window and discusses accessories, printers, online shopping, photography, music playlists, and more. 2009
Blogs, wikis, podcasts, and other powerful web tools for classrooms
By Willard H. Richardson. 2009
Richardson relates reasons he believes social Web applications and technologies are important tools for education. Provides definitions, examples, instructions, and…
references for weblogs, wikis, real simple syndication (RSS), aggregators, social bookmarking, online photo galleries, podcasting, and screencasting. Highlights social web sites such as Twitter, Flickr, YouTube, and more. 2009
How Wikipedia works: and how you can be a part of it
By Charles Matthews, Ben Yates, Chris Matthews, Phoebe Ayers, S. J. Klein. 2008
Reference guide to exploring Wikipedia, a free online encyclopedia that anyone can edit and contribute to. Provides information on evaluating…
Wikipedia articles, creating your own articles, flagging articles, importing images and media files, and understanding policies and guidelines. Includes material on the Wikimedia Foundation's sister projects--Wikibooks, Wikinews, and more. 2008
The inner history of devices
By Sherry Turkle. 2008
Thirteen essays in the form of memoirs, ethnographies, and clinical cases describe our use of technology and its impact on…
our lives and relationships. Includes the personal account of a woman with prosthetic eyes, who discusses her growing dependence on electronic devices and her changing self-image. 2008